What Is a Honeypot Trap? A Complete Guide to Cybersecurity's Sweetest Sting
Specialist in Anti-Bot Strategies
A honeypot trap is a cybersecurity mechanism that acts as a decoy to lure attackers into a controlled environment. This guide is for developers, security professionals, and anyone interested in web security.
It explains what honeypot traps are, how they work, and how they can be used to protect your systems. By understanding honeypots, you can better defend against cyber threats and gain valuable insights into attacker behavior. This article will provide you with the knowledge to identify and even implement honeypot strategies to bolster your security posture.
Key Takeaways
- What is a Honeypot Trap?: A honeypot trap is a decoy system designed to attract and trap cyber attackers, allowing security professionals to study their methods and protect real systems. This is a core concept in modern network security.
- Types of Honeypots: Honeypots are categorized by their level of interaction (low, high) and purpose (production, research), each serving different security objectives. Understanding the different honeypot types is crucial for effective threat intelligence gathering.
- Why Use Honeypots?: They are used to detect and analyze attacks, divert attackers from critical systems, and gather intelligence on emerging threats with a low rate of false positives. This makes them a key tool for proactive cybersecurity.
- Real-World Applications: Honeypots are used in various scenarios, from catching spammers with email traps to identifying vulnerabilities in corporate networks, and are a common anti-bot measure.
- Avoiding Honeypot Traps: For legitimate activities like web scraping, using tools like headless browsers and residential proxies can help avoid detection by honeypots.
What is a Honeypot Trap?
A honeypot trap is a security mechanism that creates a virtual trap to lure attackers. This intentionally compromised computer system allows security teams to study attacker behavior and improve their defenses. Honeypots are essentially decoys, designed to appear as legitimate, vulnerable systems to attract cybercriminals, diverting them from actual production systems. The primary goal of a honeypot trap is to gather threat intelligence.
The Core Concept: Luring and Learning
Honeypots function by presenting an enticing target to malicious actors. They are not meant to be secure; rather, their purpose is to be compromised. By observing how attackers interact with these fake systems, organizations gain invaluable insights into their tactics, techniques, and procedures (TTPs). This intelligence helps in strengthening real network security. For instance, a honeypot might mimic a database server, enticing an attacker to attempt SQL injection, revealing their methods without risking actual data.
Beyond Simple Decoys: A Strategic Tool
Honeypots are more than just simple traps; they are strategic tools in a comprehensive cybersecurity defense. They reduce false positives compared to traditional security measures because any activity on a honeypot is inherently suspicious, as legitimate users should not interact with it. This clear distinction makes it easier for security teams to identify and analyze genuine threats. They can be applied to various computing resources, including software, networks, file servers, and routers, making them a versatile anti-bot solution.
Types of Honeypot Deployments
Honeypots are categorized based on their purpose and level of interaction. Understanding these distinctions is crucial for effective deployment and threat intelligence gathering.
Production vs. Research Honeypots
Honeypots primarily serve two distinct purposes: production and research. Each type offers unique benefits for an organization's security posture.
- Production Honeypots: These decoys are integrated within operational networks to divert attackers from real systems. They collect data on attacks to help mitigate vulnerabilities and are often part of an intrusion detection system (IDS). Their primary goal is to enhance immediate network security by acting as a first line of defense.
- Research Honeypots: Used for educational purposes and security enhancement, these honeypots gather extensive data on attacker methodologies. They are typically more complex and are deployed by governments or large cybersecurity organizations to track advanced persistent threats and evolving hacking techniques. The focus here is on deep analysis and understanding of new threats.
Interaction Levels: Low, Medium, and High
Honeypots are also classified by their level of interaction, which dictates the amount of data they can collect and the resources they require.
- Low-Interaction Honeypots: These imitate services and systems that frequently attract criminal attention, such as common ports or vulnerable applications. They are relatively easy to set up and maintain, collecting basic information like IP addresses and attack timestamps. While they provide limited intelligence, they are effective for detecting automated attacks like botnets and worms.
- High-Interaction Honeypots: These are complex setups that behave like real production infrastructure, offering attackers extensive freedom within the decoy system. They provide deep insights into attacker techniques and motivations, but require significant maintenance and careful isolation to prevent lateral movement to real systems. Virtual machines are often used to contain these environments.
- Medium-Interaction Honeypots: Bridging the gap between low and high interaction, these honeypots simulate more services and offer a more realistic environment than low-interaction ones, without the full complexity and risk of high-interaction honeypots. They provide a good balance of data collection and ease of management.
Comparison Summary: Honeypot Types
| Feature | Production Honeypot | Research Honeypot | Low-Interaction Honeypot | High-Interaction Honeypot |
|---|---|---|---|---|
| Purpose | Divert attacks, enhance immediate security | Gather intelligence, understand new threats | Detect automated attacks, basic data collection | Deep analysis of attacker TTPs, extensive data collection |
| Complexity | Moderate | High | Low | Very High |
| Resource Needs | Moderate | High | Low | Very High |
| Risk | Lower (if properly isolated) | Higher (requires careful containment) | Low | Higher (requires careful containment) |
| Data Collected | Attack attempts, IP addresses, timestamps | Detailed TTPs, malware samples, exploit methods | IP addresses, basic attack signatures | Full attack sequences, detailed attacker behavior |
| Typical Users | Large organizations, businesses | Governments, cybersecurity researchers, intelligence agencies | Any organization for basic threat detection | Advanced security teams, research institutions |
Why Use Honeypots?
Honeypots offer significant advantages in cybersecurity, providing unique insights and protection that traditional security measures often miss. Their primary value lies in their ability to observe and learn from malicious activities in a controlled environment.
Monitoring Evolving Threats
Honeypots are invaluable for tracking the ever-changing landscape of cyber threats. They continuously gather data on new attack vectors and methodologies as they are hit by attackers. This real-time threat intelligence allows security teams to identify emerging patterns, such as new malware strains or attack origins, and adapt their defenses proactively. For example, a honeypot trap can reveal the latest techniques used in ransomware attacks, enabling organizations to update their intrusion prevention systems before a real attack occurs.
Exposing System Vulnerabilities
By analyzing how attackers exploit honeypots, organizations can pinpoint weaknesses in their own systems. This low-risk method of vulnerability assessment helps in understanding which exploits are most commonly used and how to patch them effectively. A company might deploy a honeypot mimicking an old server to see if it attracts specific exploits, thereby identifying a critical vulnerability in their legacy systems that needs immediate attention.
Identifying Insider Threats
Honeypots can also be deployed to detect and deter insider threats. By placing decoy data or systems that only an insider with specific access or knowledge would attempt to compromise, organizations can identify malicious internal actors. This is particularly useful in environments where disgruntled employees or compromised accounts pose a significant risk. For instance, a honeypot designed to look like a sensitive HR database could expose an employee attempting unauthorized data exfiltration.
Low False-Positive Rate
Unlike many security tools that generate numerous alerts, honeypots have an exceptionally low false-positive rate. Any interaction with a honeypot is by definition unauthorized, as legitimate users have no reason to access it. This clarity allows security teams to focus their resources on genuine threats, reducing alert fatigue and improving response efficiency. This makes them a cost-effective defense, as less time is spent sifting through irrelevant data.
Essential Training Tool
Honeypots serve as an excellent training ground for cybersecurity professionals. By analyzing real attack data captured by honeypots, security personnel can gain practical experience in threat analysis and incident response. This hands-on learning is crucial for staying current with new and evolving online threats, preparing teams for real-world cyber confrontations.
Real-World Examples and Application Scenarios
Honeypots are not just theoretical constructs; they are actively deployed in various real-world scenarios to combat cybercrime and gather intelligence. These examples highlight their versatility and effectiveness.
Catching Cybercriminals in the Act
One notable example involved security researchers setting up a clever honeypot trap that tricked hackers into revealing their secrets. This honeypot, designed to look like a vulnerable remote machine, recorded every move cybercriminals made, including their login details. This provided invaluable threat intelligence on their methods and allowed for better understanding of their attack patterns. Such operations are critical for developing more robust defenses against sophisticated adversaries.
Protecting Against Web Scraping
Honeypots are also widely used to detect and deter malicious web scraping activities. Websites often embed hidden links or fields that are invisible to legitimate users but are easily detected by automated web scrapers or bots. When a bot interacts with these hidden elements, it triggers an alert, identifying the activity as suspicious. This allows website administrators to block the offending IP address or implement further countermeasures. For instance, an e-commerce site might use a honeypot to identify bots attempting to scrape product prices or inventory levels, protecting their competitive edge.
Combating Spam and Malware
Email honeypots, often called spam traps, are fake email addresses strategically placed to attract spammers. Since legitimate users would not send emails to these addresses, any incoming mail is automatically flagged as spam. This helps Internet Service Providers (ISPs) and email security companies identify spam sources and block them, significantly reducing the amount of junk mail in inboxes.
Similarly, malware honeypots mimic software applications or APIs to attract malware, allowing security researchers to analyze new strains in a controlled environment and develop effective countermeasures. This proactive approach is vital in the ongoing fight against evolving malware threats.
University Honeypot Deployments
Universities often deploy honeypots for research and educational purposes. A case study on deploying a university honeypot demonstrated its effectiveness in understanding attack patterns targeting academic networks.
These deployments provide students and researchers with hands-on experience in cybersecurity, allowing them to analyze real-time attacks and contribute to the development of new defense strategies. This practical application of honeypot technology helps bridge the gap between theoretical knowledge and real-world cybersecurity challenges.
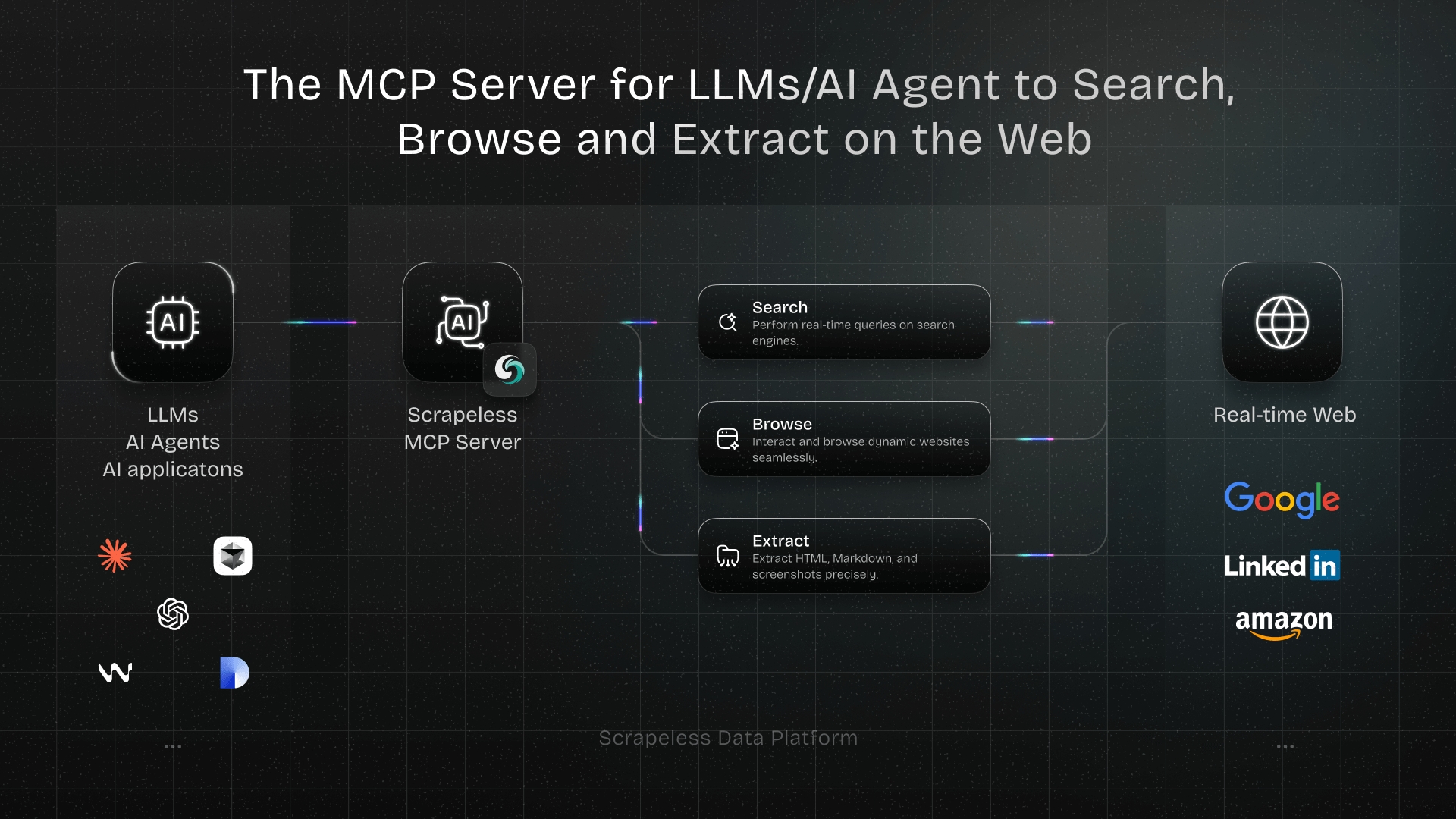
Scrapeless: Bypassing Anti-Bot Measures
While honeypots are effective at catching malicious actors, legitimate web scraping for data collection can sometimes trigger these defenses. This is where services like Scrapeless become invaluable. Scrapeless is designed to help users bypass sophisticated anti-bot measures, including Cloudflare, DataDome, and other anti-robot systems, ensuring uninterrupted access to public web data. It allows ethical users to gather necessary information without being blocked, providing a seamless scraping experience.
If you're looking to gather data without being flagged by honeypots or other anti-bot mechanisms, consider trying Scrapeless. It helps you navigate the complexities of web data extraction efficiently and reliably. Try Scrapeless for free.
Key Advantages and Technical Capabilities of Scrapeless
🚀 Advanced Anti-Bot Evasion: Effectively bypasses Cloudflare, DataDome,and other major protection systems.
🧠 Human-Like Interaction: Leverages dynamic request handling and smart fingerprinting to mimic real user behavior.
🔒 High Anonymity: Multi-layer proxy rotation and encryption help avoid IP bans and traffic fingerprinting.
📊 High Success Rates: Ensures consistent data extraction even from websites with strict security defenses.
⚙️ Easy Integration: Offers APIs and SDKs that integrate seamlessly with common scraping frameworks and workflows.
🌍 Global Coverage: Provides geo-distributed exit nodes to support international and region-specific data collection.
Legal and Ethical Considerations in Different Countries
Honeypot deployment and web scraping can have different legal implications depending on the country. Understanding local laws ensures that your cybersecurity or data collection activities remain compliant.
🇺🇸 United States
In the U.S., the Computer Fraud and Abuse Act (CFAA) governs unauthorized access to computer systems. The landmark case hiQ Labs v. LinkedIn clarified that scraping publicly available data does not violate the CFAA, provided you do not bypass login protections or access controls.
Key considerations:
- Scraping public pages is generally legal.
- Violating terms of service or copyright laws (e.g., DMCA) may still trigger civil liability.
- Honeypots should be deployed ethically to avoid legal exposure.
🇬🇧 United Kingdom
The Computer Misuse Act 1990 prohibits unauthorized access to computer systems. UK courts evaluate whether access is “unauthorized” or abusive.
Key considerations:
- Scraping publicly available data carries low risk.
- Excessive automated requests may be considered misuse.
- Honeypots help detect unauthorized activities, providing legal evidence for misuse cases.
🇪🇺 European Union
The General Data Protection Regulation (GDPR) regulates personal data handling. Any scraping involving personal information—like seller profiles or reviewer names—requires consent.
Key considerations:
- Public factual data (prices, ratings) is generally acceptable.
- Personal data collection must comply with GDPR requirements.
- Honeypots must be carefully configured to avoid collecting private EU data inadvertently.
🇯🇵 Japan
Japan’s Unauthorized Access Prohibition Act criminalizes bypassing access controls on computer systems. Automated access without permission is highly sensitive.
Key considerations:
- Honeypots should be clearly isolated.
- Avoid bypassing login or authentication systems.
- Observing attacker behavior in a controlled environment is acceptable for research and security purposes.
🇰🇷 South Korea
The Act on Promotion of Information and Communications Network Utilization and Information Protection strictly regulates unauthorized data collection, especially for commercial use.
Key considerations:
- Public data scraping is allowed if not used for profit or harm.
- Commercial or large-scale scraping may require explicit permission.
- Honeypots are effective for detecting malicious actors within these regulatory limits.
🌍 Africa
Most African countries do not have explicit web scraping laws. However, some nations have data protection laws (e.g., South Africa’s POPIA) that govern personal data.
Key considerations:
- Scraping public, non-personal data is generally safe.
- Collecting personal information may require compliance with local regulations.
- Honeypots can help monitor and prevent unauthorized access across networks.
Conclusion
Honeypot traps are an indispensable tool in the modern cybersecurity landscape. They serve as effective decoys, diverting malicious actors from critical systems and providing invaluable threat intelligence on their evolving tactics. By deploying various honeypot types, organizations can proactively identify vulnerabilities, monitor emerging threats, and even detect insider risks. The insights gained from honeypot interactions enable security teams to build more resilient defenses and stay ahead of cybercriminals.
For those engaged in legitimate data collection, navigating the complex world of anti-bot measures and honeypots can be challenging. Scrapeless offers a robust solution, allowing you to bypass these sophisticated defenses and access the data you need without interruption. Its ability to circumvent Cloudflare, DataDome, and other anti-robot systems makes it an essential tool for ethical web scraping.
Ready to enhance your data collection capabilities and avoid honeypot pitfalls?
Recommended Reading
Q1: What is the primary purpose of a honeypot trap?
A1: The primary purpose of a honeypot trap is to act as a decoy system to lure and trap cyber attackers. This allows security professionals to observe their methods, gather threat intelligence, and divert them from real, critical systems, thereby enhancing overall network security.
Q2: How do low-interaction honeypots differ from high-interaction honeypots?
A2: Low-interaction honeypots simulate only basic services and collect limited data, making them easy to deploy but providing less insight into complex attack patterns. High-interaction honeypots mimic full production systems, offering extensive data on attacker behavior but requiring more resources and careful management due to higher risk. Both are important honeypot types for different security objectives.
Q3: Can honeypots detect insider threats?
A3: Yes, honeypots can be designed to identify insider threats. By placing decoy data or systems that only an insider with specific knowledge or access would attempt to compromise, organizations can detect and analyze malicious activities from within their network, strengthening their internal cybersecurity posture.
Q4: Are honeypots effective against all types of cyberattacks?
A4: While highly effective for gathering threat intelligence and diverting certain types of attacks, honeypots are not a standalone solution. They are best used as part of a comprehensive cybersecurity strategy, complementing other security measures to provide a layered defense against a wide range of threats.
Q5: How can legitimate web scrapers avoid honeypot traps?
A5: Legitimate web scrapers can avoid honeypot traps by using advanced tools and techniques such as headless browsers, rotating residential proxies, and reliable web scraping services like Scrapeless, which are designed to bypass anti-bot measures without triggering alarms.
References
[1] Imperva. (n.d.). What is a Honeypot | Honeynets, Spam Traps & more.
[2] CrowdStrike. (2025, January 16). What is a Honeypot in Cybersecurity?.
[3] AVG Antivirus. (2024, January 7). What Is a Honeypot? Cybersecurity Traps Explained.
[4] IPRoyal. (2024, February 26). The Ultimate Guide to Honeypot Traps: All You Need to Know.
[5] Akamai. (2019, January 3). Low, Medium and High Interaction Honeypot Security.
[6] Wired. (2023, August 9). A Clever Honeypot Tricked Hackers Into Revealing Their Secrets.
[7] ZenRows. (2022, November 17). What Is a Honeypot Trap and How to Bypass It.
[8] CEUR-WS. (n.d.). Deploying a University Honeypot: A case study.
Recommended
At Scrapeless, we only access publicly available data while strictly complying with applicable laws, regulations, and website privacy policies. The content in this blog is for demonstration purposes only and does not involve any illegal or infringing activities. We make no guarantees and disclaim all liability for the use of information from this blog or third-party links. Before engaging in any scraping activities, consult your legal advisor and review the target website's terms of service or obtain the necessary permissions.